How to Authenticate and Scope Multi-Tenant Vitals API Requests
Learn how multi-tenant vitals API authentication and scoping works, from OAuth 2.0 token flows to tenant isolation patterns that keep health data where it belongs.
How to authenticate and scope multi-tenant vitals API requests
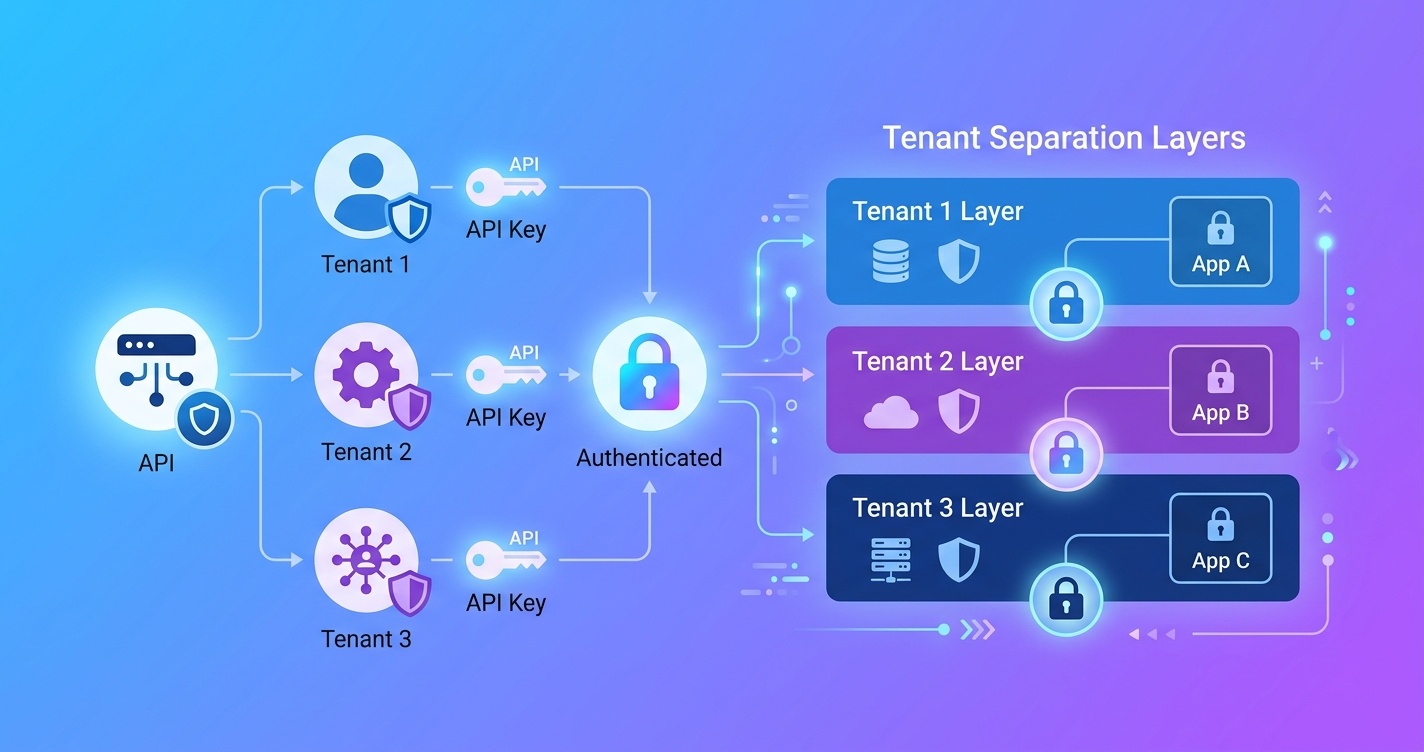
When a vitals API serves more than one organization, the authentication layer has to answer two questions at once: who is making this request, and which tenant's data should they be allowed to touch? Get either answer wrong and you have a data breach. Get both right but slowly and your API becomes unusable for real-time health monitoring. Multi-tenant vitals API authentication and scoping is one of those problems that looks straightforward on a whiteboard but gets complicated fast once you factor in regulatory requirements, varying permission models per tenant, and the fact that vital signs data is about as sensitive as health data gets.
"Nearly 90% of non-federal acute care hospitals in the United States now use APIs to enable patient access to their health data through apps, and more than two-thirds have adopted FHIR APIs specifically." — U.S. Office of the National Coordinator for Health IT (ONC), 2025
That adoption rate means more health platforms are building multi-tenant API layers than ever before. The infrastructure patterns are maturing, but the details still trip people up.
Why vitals APIs need tenant-aware authentication
A single-tenant API can get away with simpler auth. One API key, one set of permissions, one data store. Multi-tenant changes the math entirely.
Consider a vitals API that serves three customers: a telehealth platform capturing heart rate during video visits, a corporate wellness provider running biometric screenings, and a clinical research organization collecting respiratory rate data across trial sites. Each tenant has different data retention policies, different compliance requirements, and different ideas about who within their organization should access what.
The authentication system has to enforce all of this without becoming a bottleneck on every API call. A 2024 analysis by Health-Samurai, a health IT infrastructure consultancy, found that multi-tenant FHIR API designs require dedicated authentication server instances per tenant, each with its own base URL, to properly isolate authorization contexts. Sharing a single auth server across tenants creates cross-contamination risks that are difficult to audit.
| Authentication pattern | Tenant isolation | Complexity | Latency per request | Best for |
|---|---|---|---|---|
| API key per tenant | Weak — key rotation affects all users | Low | <5ms lookup | Internal tools, dev/staging |
| OAuth 2.0 with tenant-scoped tokens | Strong — tokens carry tenant context | Medium | 10-30ms token validation | Production multi-tenant APIs |
| OAuth 2.0 + SMART on FHIR scopes | Strong — clinical-grade isolation | High | 20-50ms with scope validation | Health systems, EHR integrations |
| Mutual TLS + JWT | Very strong — certificate-level trust | High | 15-40ms handshake + validation | Enterprise B2B, regulated environments |
| Dedicated auth server per tenant | Strongest — full separation | Very high | Varies by implementation | Large health system deployments |
OAuth 2.0 token flows for multi-tenant vitals
OAuth 2.0 is the de facto standard here, but vanilla OAuth does not know anything about tenants. You have to build that awareness into the token itself.
The most common approach embeds a tenant_id claim in the JWT access token. When a developer's application authenticates against your authorization server, the token it receives carries both the identity of the caller and the tenant they belong to. Every API endpoint then validates both before doing anything.
A typical token payload for a multi-tenant vitals API looks something like this:
{
"sub": "app-id-7f3a9b",
"tenant_id": "tenant-acme-health",
"scopes": ["vitals:read", "vitals:write", "users:read"],
"aud": "https://api.example.com/v1",
"exp": 1744398000,
"iss": "https://auth.example.com"
}
The scopes array controls what operations the token holder can perform. The tenant_id controls which slice of data they can see. Both get checked on every request. Drop either check and you have a problem.
One detail that catches people: the authorization server itself needs to be multi-tenant aware. Auth0's developer community documentation from 2022 (still referenced widely in 2026) walks through the challenge of issuing client credentials in a multi-tenant setup where each tenant expects isolated API access but shares the same underlying auth infrastructure. The solution generally involves either tenant-specific OAuth applications or a shared application with tenant claims injected at token issuance.
Scoping strategies that actually work
Scoping is where things get granular. A scope like vitals:read is too broad for most production deployments. Real-world vitals APIs need scopes that reflect both the data type and the context.
Here is how scoping typically breaks down for a multi-tenant vitals platform:
Resource-level scopes control access to specific data types:
vitals.heart_rate:read— can read heart rate measurementsvitals.respiratory_rate:read— can read respiratory ratevitals.spo2:read— can read blood oxygen estimatesvitals.all:write— can submit new vital sign measurements
Organizational scopes control the blast radius:
org:self— access only your own tenant's dataorg:delegated— access data from tenants who have granted you permission (useful for aggregators or research platforms)
Operational scopes control what you can do beyond CRUD:
analytics:read— access aggregate reportsexport:bulk— run data exportsadmin:users— manage API users within a tenant
The SMART on FHIR framework, originally developed by Harvard Medical School's computational health informatics program and Boston Children's Hospital, takes this further with clinical scopes. SMART scopes follow the pattern [patient|user|system]/[ResourceType].[read|write|*], which maps well to vitals data. A 2025 security best practices guide published by Kodjin, a FHIR infrastructure provider, noted that combining OAuth 2.0 with SMART on FHIR scopes provides "secure, scalable integration of third-party applications while maintaining strict control over sensitive healthcare data access."
Tenant isolation at the data layer
Authentication and scoping handle the request side. But the data layer needs its own isolation guarantees. If a valid token for Tenant A can somehow query Tenant B's vital signs because of a missing WHERE clause, the auth layer did its job and the system still failed.
There are three common patterns:
Schema-per-tenant gives each tenant their own database schema. Queries are physically unable to cross tenant boundaries because the tables are separate. This is the most secure but gets expensive with hundreds of tenants and makes schema migrations painful.
Row-level security with tenant column adds a tenant_id to every table and enforces filtering at the database level. PostgreSQL's row-level security policies are commonly used here. The application does not even need to remember to filter — the database rejects cross-tenant queries automatically. AWS published a detailed architecture guide in 2024 for building multi-tenant FHIR servers with AWS HealthLake that uses this approach, combining SigV4 authentication with tenant-scoped data partitions.
Separate databases per tenant is the nuclear option. Full physical isolation. Some regulated health platforms use this because it simplifies compliance auditing: you can point an auditor at one database and say "this is all of Tenant X's data, nothing else."
| Isolation model | Security | Cost at scale | Migration complexity | Audit simplicity |
|---|---|---|---|---|
| Schema-per-tenant | High | Medium | Hard — N schemas to migrate | Good — clear boundaries |
| Row-level security | Medium-high | Low | Easy — one schema | Moderate — requires query audit |
| Database-per-tenant | Highest | High | Very hard — N databases | Best — physical separation |
Rate limiting and abuse prevention per tenant
Multi-tenant vitals APIs also need tenant-aware rate limiting. A global rate limit does not work because one noisy tenant can starve the others. Each tenant needs its own allocation based on their plan, their expected volume, and the specific endpoints they are hitting.
Vital signs endpoints have different cost profiles. A simple GET for a single heart rate reading is cheap. A bulk export of six months of respiratory rate data for a clinical trial is expensive. Rate limits should reflect this.
A common implementation uses a sliding window counter keyed on {tenant_id}:{endpoint_category}. Redis or similar in-memory stores handle the counting. When a tenant exceeds their limit, the API returns a 429 with a Retry-After header and a response body that specifies which limit was hit. This matters because a developer debugging a rate limit issue needs to know whether they hit their per-second burst limit or their daily export quota.
DreamFactory, an API management platform, published a 2024 analysis of fine-grained API access with OAuth claims in multi-tenant setups. Their recommendation: embed rate limit tier information directly in the JWT claims so the API gateway can enforce limits without a database lookup on every request. This moves the rate limit check to the edge, which reduces latency on the hot path.
Handling cross-tenant access
Some use cases legitimately require cross-tenant access. A research platform might aggregate anonymized vital signs across multiple participating health systems. An insurance carrier might need to query vitals data from several wellness providers. A parent company might want a unified dashboard across subsidiary tenants.
Cross-tenant access should never be implicit. It requires explicit grants, typically modeled as delegation relationships in the authorization system. Tenant A grants Tenant B access to a specific scope for a defined time period. The resulting tokens carry both the caller's identity and the delegating tenant's context.
{
"sub": "app-id-research-platform",
"tenant_id": "tenant-research-org",
"delegated_access": [
{
"tenant_id": "tenant-hospital-a",
"scopes": ["vitals.heart_rate:read"],
"expires": "2026-12-31T23:59:59Z"
}
]
}
The API layer checks both the primary tenant context and any delegated grants. This keeps the access auditable and revocable.
Audit logging for compliance
Every authenticated API request to a multi-tenant vitals platform should produce an audit log entry. HIPAA requires it. SOC 2 requires it. And honestly, when something goes wrong at 2am and you need to figure out which tenant's API key made that suspicious bulk export, you will be glad you have it.
Each log entry should capture the tenant ID, the authenticated identity, the requested scope, whether the request was allowed or denied, and a timestamp. For vitals data specifically, the Accountable HQ security guide (2025) recommends also logging the patient and encounter context with every API call to maintain accurate audit trails that satisfy HIPAA's access logging requirements.
Store audit logs in an append-only system separate from the main application database. Tenants should be able to query their own audit logs through the API, but never another tenant's.
Current research and evidence
The SMART Health IT project at Harvard continues to push the standards forward. Their 2025 commentary noted that the average U.S. patient can now connect apps directly to their electronic medical records, which means the API layer between apps and data is carrying more traffic and more sensitive data than ever before.
On the infrastructure side, Emorphis Health published a 2025 analysis of SMART on FHIR adoption showing that the framework's OAuth 2.0 integration has become the baseline expectation for health data APIs, not a nice-to-have. Organizations building vitals APIs without SMART-compatible scoping are finding themselves locked out of health system integrations.
The Old City Publishing journal Ad Hoc & Sensor Wireless Networks featured research in 2024 on securing health data collected from body area networks, noting that multi-tenant architectures require "effective leveraging for legitimate medical research and data analysis purposes" while maintaining strict access controls. The tension between data utility and data isolation remains the core engineering challenge.
The future of multi-tenant vitals API security
Two trends are converging that will shape how multi-tenant vitals APIs handle auth in the next few years.
First, on-device processing is reducing the amount of raw video that ever leaves the user's phone. When the rPPG signal extraction happens client-side and only computed vital signs hit the API, the authentication model shifts. You are protecting numerical health metrics rather than biometric video, which changes the risk profile and potentially the regulatory treatment.
Second, verifiable credentials and decentralized identity are starting to show up in health tech specifications. Instead of a centralized OAuth server deciding who can access what, the tenant themselves could issue cryptographic credentials that the API validates independently. This is still early, but pilot programs in the EU's European Health Data Space are testing exactly this pattern for cross-border health data access.
For platform builders today, the practical advice is to start with OAuth 2.0 and tenant-scoped JWTs, add SMART on FHIR scopes if you are integrating with health systems, and architect your data layer for row-level security with a clear path to schema-per-tenant if a customer requires it. Circadify's API platform, for example, is built around these principles, offering developer tools at circadify.com/custom-builds for teams building multi-tenant health integrations.
Frequently asked questions
What is the difference between authentication and scoping in a multi-tenant API?
Authentication verifies identity: who is making the request. Scoping controls authorization: what they are allowed to do. In a multi-tenant vitals API, authentication confirms the caller and their tenant, while scoping determines which vital sign types, operations, and data partitions they can access. Both are checked on every request.
Can I use API keys instead of OAuth for a multi-tenant vitals API?
You can, but you probably should not in production. API keys do not carry tenant context, scopes, or expiration by default. You end up building all of that logic into your application layer instead of leveraging standard token claims. API keys work fine for internal tools and development environments. For production multi-tenant health data, OAuth 2.0 with JWT tokens is the standard.
How does SMART on FHIR relate to multi-tenant API scoping?
SMART on FHIR is a framework built on OAuth 2.0 that adds clinical-specific scopes and launch contexts. It was designed for exactly this kind of problem: multiple applications accessing health data through a shared API layer with fine-grained permissions. If your vitals API needs to integrate with EHR systems or health platforms, supporting SMART scopes will make those integrations significantly easier.
What happens if a tenant's API credentials are compromised?
With properly scoped tokens, the blast radius is limited to that tenant's data. This is the whole point of tenant isolation. You revoke the compromised credentials, rotate the tenant's API keys or client secrets, review audit logs for unauthorized access, and notify the affected tenant. If you built your system with database-level tenant isolation, you can be confident that other tenants' data was not exposed.
You can also read about related patterns in our post on what is an rPPG API and its architecture and how REST vs WebSocket approaches affect multi-tenant streaming designs.
